Enhance Security by Removing Limits
SIEMs have historically done well in helping organizations detect threats. Modern threat activity has shown, however, that tracking pre-selected data and relying on IOCs (indicators of compromise) isn't enough to protect business from attackers. Threat hunting and going off the rails of "pre-fabbed search" are absolutely critical to defending organizations. You don't have to read very much Sun Tzu to learn the importance of "Know Thyself" and defenders advantage. SIEMs have let us down in this area. Gravwell provides a solution that removes limits and puts you in control of what data you can collect, and what questions you can ask.
Gravwell is an unstructured data lake built from scratch to address modern data collection and interrogation requirements. It handles common things like syslog, Windows events, and firewall logs. Gravwell is also very comfortable gettin' weird to support data in native format like custom application logs, PCAP, netflow, or even images and audio.
How can you add threat hunting capability to your current SIEM? The basic process is similar regardless of which products are currently being used, but Gravwell is great at molding space to your unique organizational needs. We'll break down the steps below:
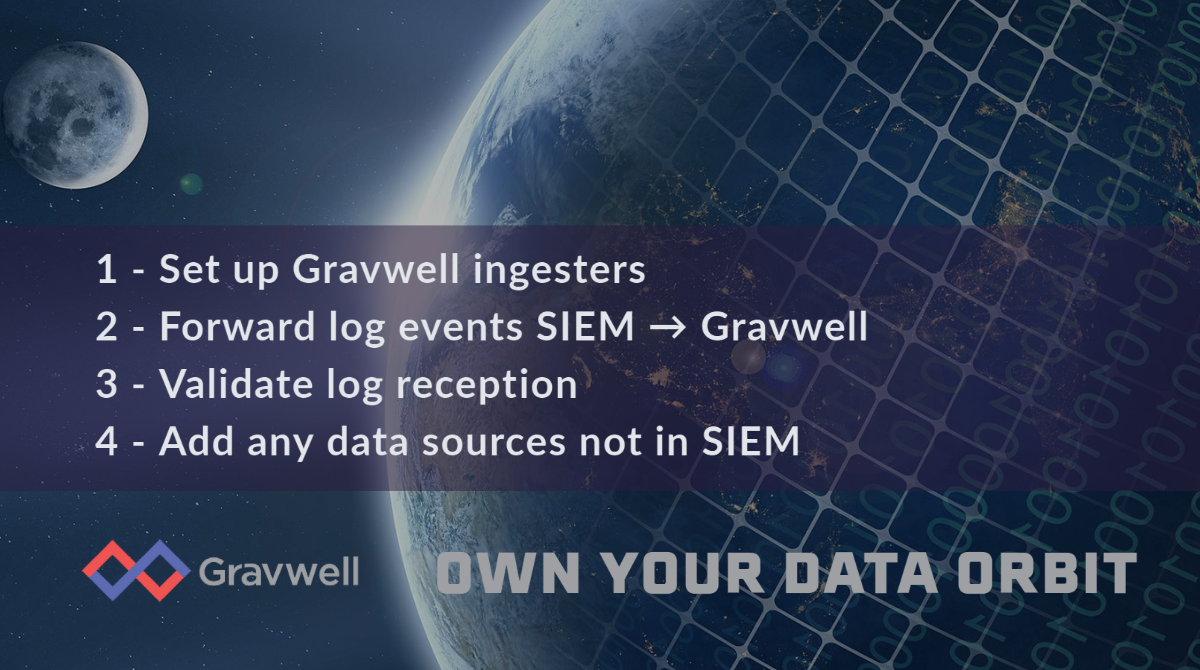
- Establish a Gravwell system with event ingesters
- Forward log events from the SIEM into Gravwell
- Validate log reception
- Add additional data sources not supported by SIEM
Establish a Gravwell system with event ingesters
Setting up a Gravwell instance is (for small deployments) as simple as `apt install gravwell`. This is made possible by our unified architecture and ingest framework. We didn't glue 80 different open source solutions together -- Gravwell is purpose-built. We have made our ingesters open source to put more control in the hands of our customers and remove limits. And since Gravwell is an unstructured data lake, you don't have to know anything about your data before you collect it.
Forward log events from the SIEM into Gravwell
Most SIEMs support log forwarding capabilities. It's usually as simple as entering a configuration menu and inputting the Gravwell address for log forwarding collection. In the event that a SIEM doesn't have such an option, our open source ingestion framework makes it easy to build one, or better yet, engage our world-class engineers to build one for you.
Validate log reception
It's easy to determine whether logs are making it into the Gravwell platform and issues at this stage are very rare, outside of standard network and firewall configuration. One major advantage of Gravwell is the ability to collect any data, of any size, and any format. Our hybrid indexing stores and catalogues the data for rapid search without you needing to define a schema or format structure. This capability is especially necessary for those situations where there is no such thing as structure or when we have unintended structure nesting. Take, for example, tunneling over DNS -- a very common attacker egress and evasion technique. Gravwell builds a search pipeline as a series of analysis modules, and so pulling the payload from DNS and feeding that back into a packet dissection module or a decryption module is very powerful, despite it being easy.
Add additional data sources not supported by SIEM
Threat hunting requires a lot of data sources, and it requires the raw entries. SIEM events typically are normalized and taxonomized, which results in information loss. When you're investigating a potential breach, the worst thing to discover is that a SIEM saw the events that could help you resolve the issue, but threw them away. Gravwell enables collection and correlation of a wide variety of events from a wide variety of sources, and any security team is better served by having greater observability.
Talk to a Gravwell consultant to get started
Every organization is unique and every SIEM has a different way of exporting events. The Gravwell staff are absolutely out of this world and really enjoy conversations about collecting more data. Reach out to us to chat about how threat hunting capability could be much closer than light years away.


