You never forget the first time… and we’ll always remember getting together with hundreds of leading security experts at the first ever Wild West Hacking Fest in Deadwood, South Dakota. We got a lot of praise before the first guest arrived at our table, but that’s probably because we sponsored the coffee! Still, when people came over to look at Gravwell’s products, we got a lot of positive feedback and eager experts wanting to test what we can do.
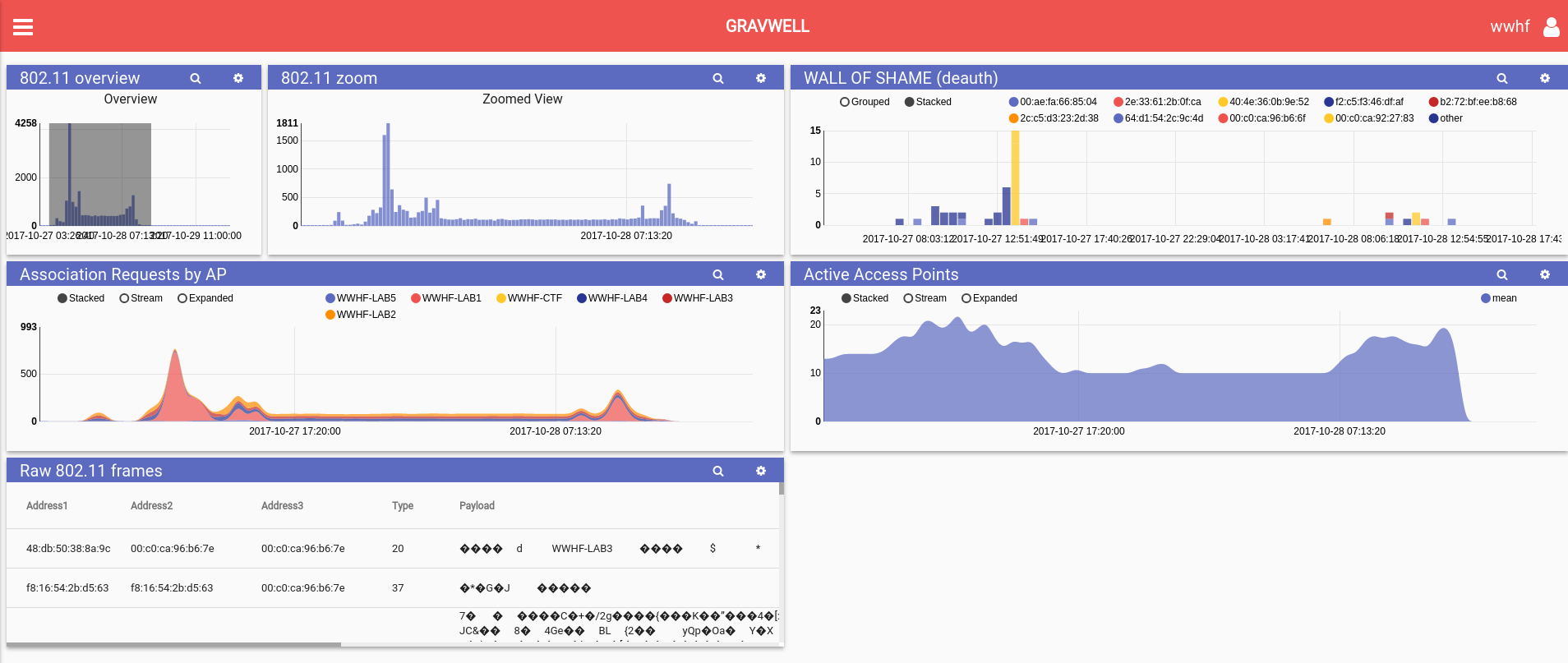
For example, our table neighbors from Black Hills Information Security brought a wireless hacking challenge. They loaned us a few antennas and we demonstrated how our data analysis product could help identify a DOS attack at the conference, which they were concerned about as it would prevent everyone from participating. We built a dashboard and provided some search capability on raw 802.11 frames.
We provided detailed analytics for the wireless challenge… here’s a look at some of the material we gathered during the event:
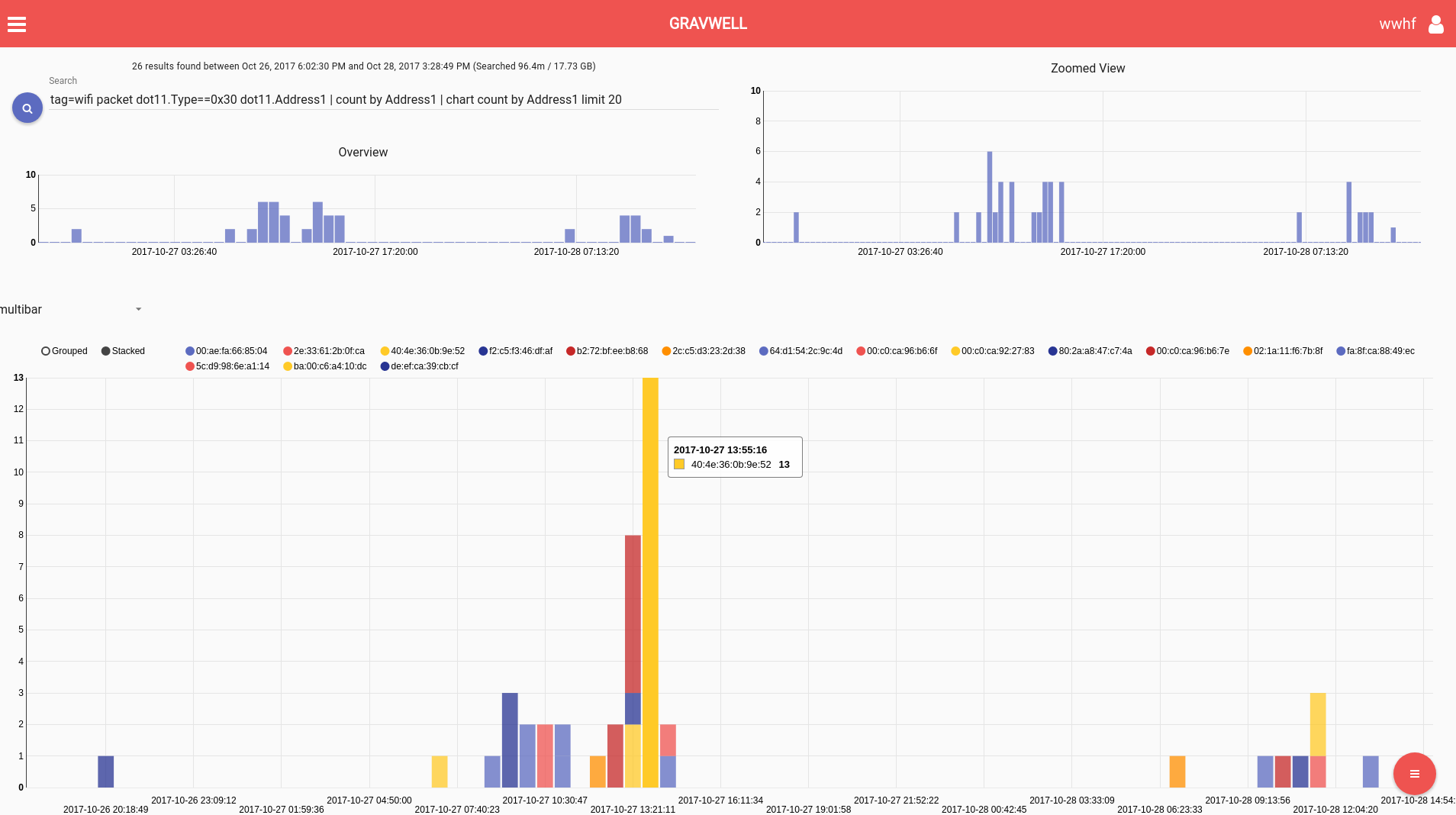
First, we helped the BHIS folks monitor the challenge for anyone sending Deauth packets. In short, deauth messages tell clients to disassociate (and reassociate) with the access point. It’s common for some attacks to do this in order to generate more information to aid cracking cryptography. For this event, these were entirely unnecessary and could prevent people from participating in the challenge. Similarly, these packets should be quite rare in an enterprise environment and monitoring them is an important defensive activity.
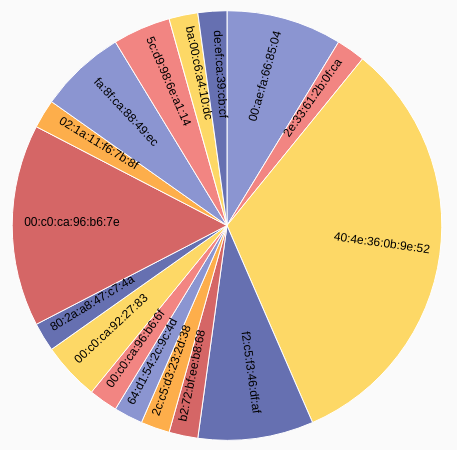
The following screenshots show the “Wall of Shame” -- MAC addresses sending deauth packets over time, and then a pie chart of the total deauth packets.
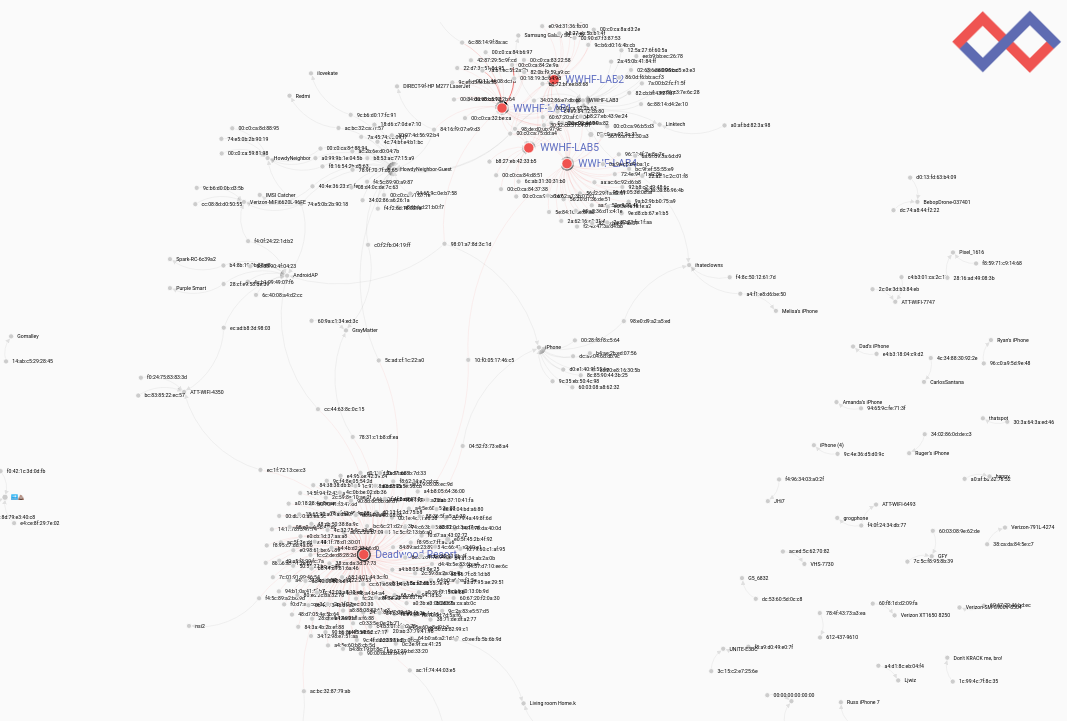
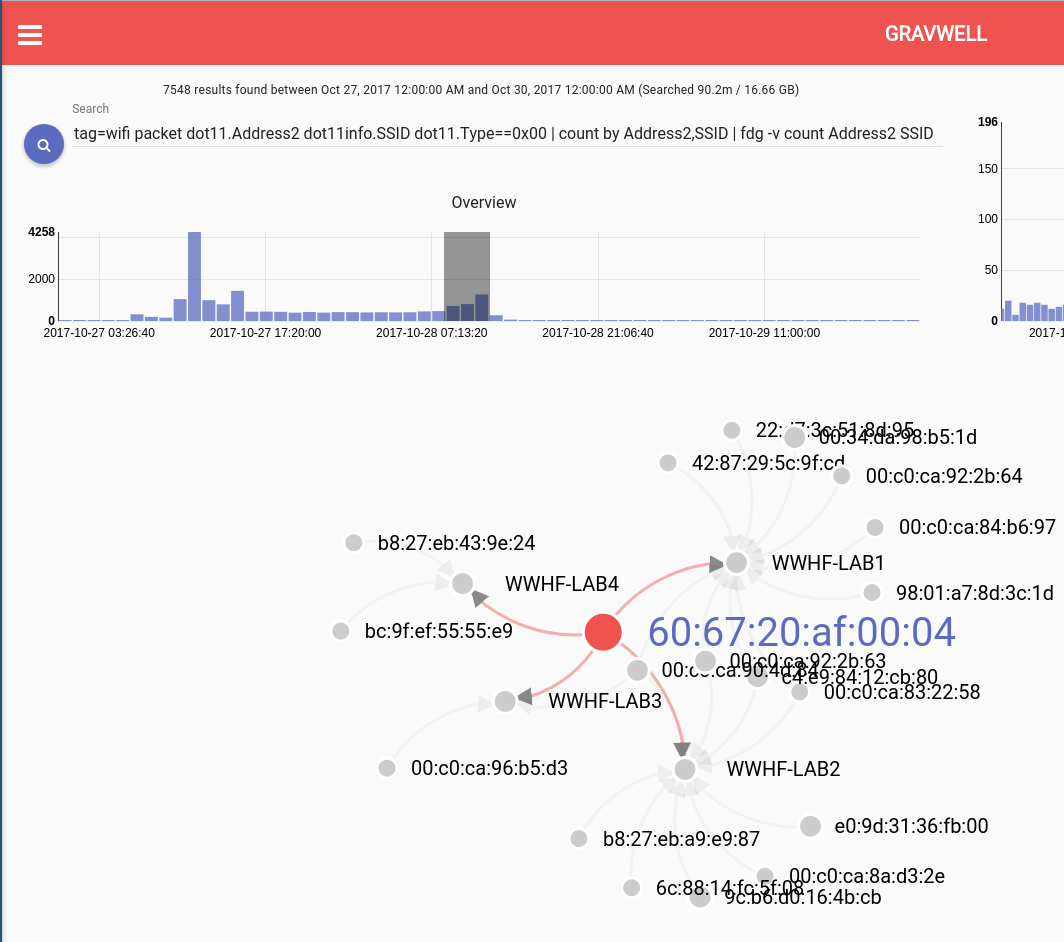
Secondarily, the BHIS team wanted some high level views of what was happening with the wireless network. We built out a search that generates a live force directed graph of all wifi associations. The patterns that stand out are interesting. In this graph you can see the wireless challenge labs at the top and the large cluster at the bottom is the Deadwood lodge convention center wifi. Then, smattered about are various iphones, hotspots, and other sparse activity.
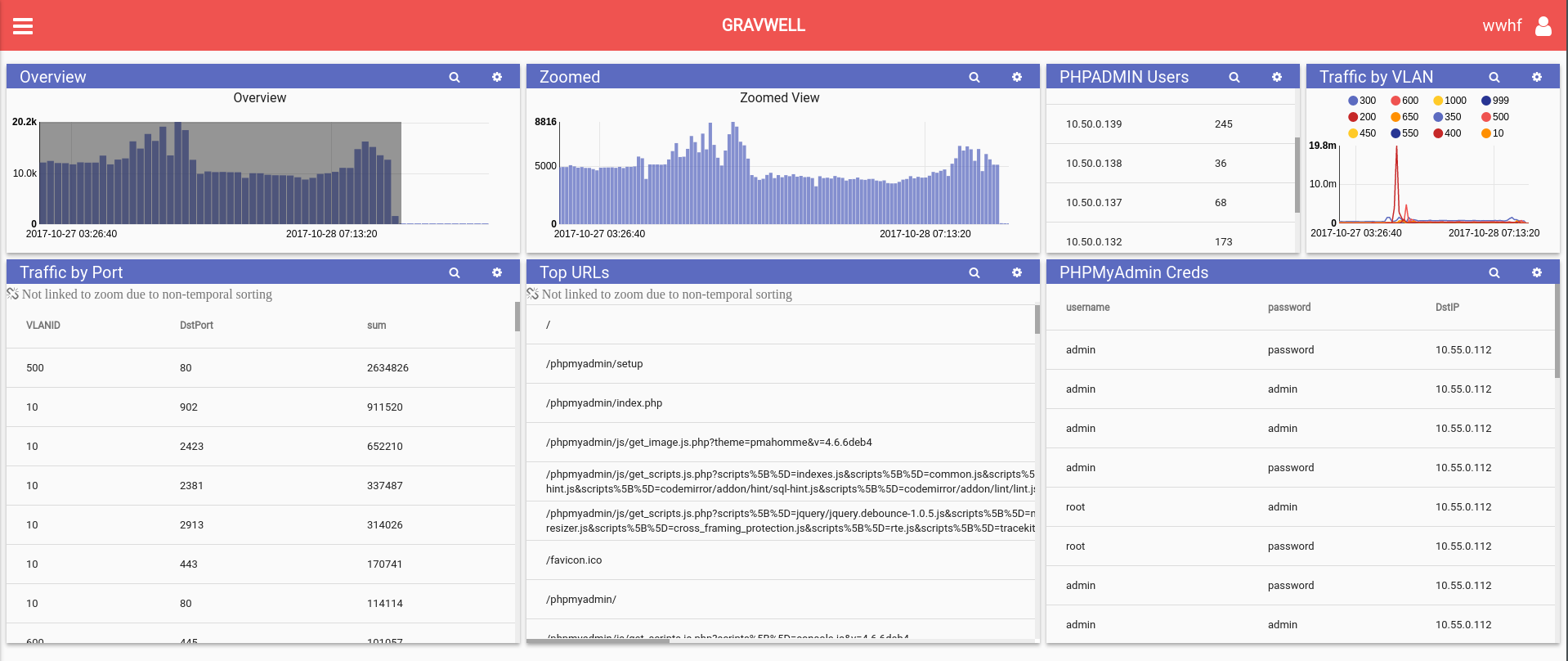
We built a dashboard to track active access points seen at a given time, association requests by AP, and other wireless data. Additionally, we ingested a span port from the BHIS switch which allowed us to correlate wifi activity with network activity and observe participants going through the challenge (see our previous post for low level network analytics). One dashboard we built harvested credentials being submitted in plaintext over http during the contest.
Using Gravwell, we can go back in time and always have access to the underlying data. During the event we had a dashboard actively running showing us what was going on. Here’s a screenshot of the FDG zoomed in on a smaller period of time. You can see the MAC address in the middle belonging to the winner of the contest. The lines demonstrate his progress as he spent time on each WWHF-LAB access point to finish the challenges.
The BHIS wifi hacking exercise was a big hit and I heard a lot of participants thanking them for the lessons learned. We personally learned that SSIDs can contain unicode characters which we discovered when we saw emoji results in our list of all SSIDs present. Whoever set up this AP, we love you.
If you're interested in using Gravwell for doing wifi analytics in your own organization, hit that request trial button to reach out.
Working with the security experts who were “keeping an eye” on what was happening around us, we felt like we weren’t just there selling our tool anymore. We were there connecting with the community. We came away not just with interested potential customers, but with new ideas on how our products could be used to identify attacks, aggregate data on those attacks, and supply the good guys with information used to protect others from dangerous activity.
Wild West Hackin’ Fest has already announced continuation for 2018 and you can bet yer boots that Gravwell will be there again with some exciting hands-on hunting exercises and prizes for those who complete them….and of course, more coffee.