In our first part of the WTF Windows!?!?! Query of the Week, we are going to jump into a fun hunt. Long story short, we had some system applications that were hanging, Windows has an event for this 1002. Great, lets go see why they were hanging!
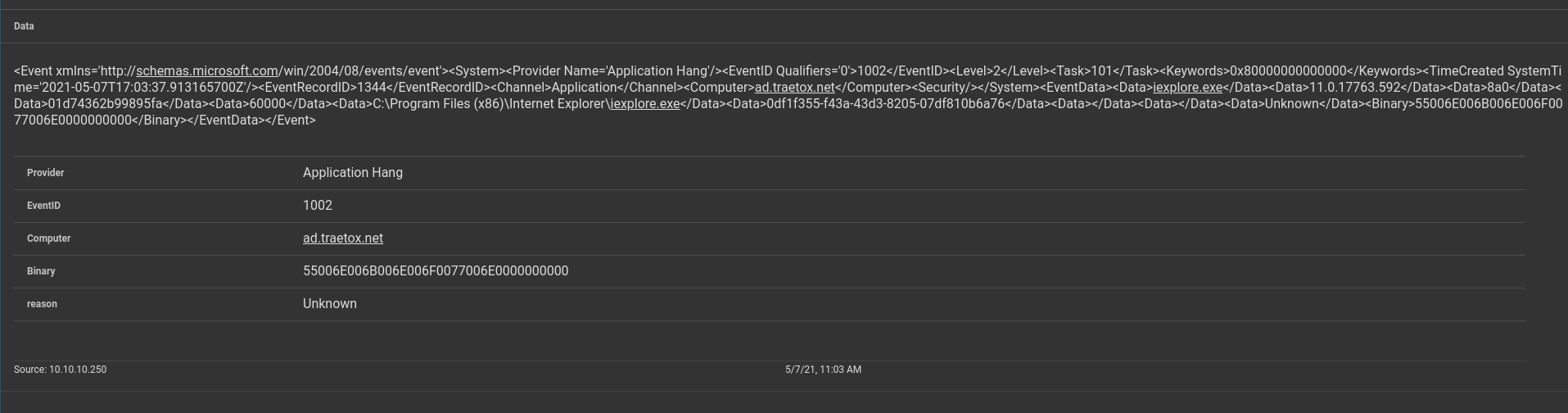
The Raw Log
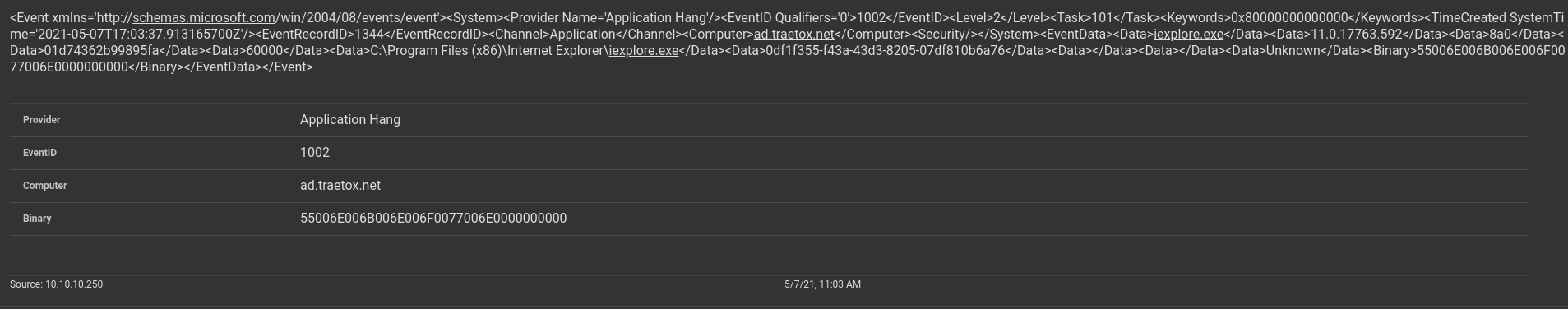
<Event xmlns='http://schemas.microsoft.com/win/2004/08/events/event'><System><Provider Name='Application Hang'/><EventID Qualifiers='0'>1002</EventID><Level>2</Level><Task>101</Task><Keywords>0x80000000000000</Keywords><TimeCreated SystemTime='2021-05-07T17:03:37.913165700Z'/><EventRecordID>1344</EventRecordID><Channel>Application</Channel><Computer>ad.traetox.net</Computer><Security/></System><EventData><Data>iexplore.exe</Data><Data>11.0.17763.592</Data><Data>8a0</Data><Data>01d74362b99895fa</Data><Data>60000</Data><Data>C:\Program Files (x86)\Internet Explorer\iexplore.exe</Data><Data>0df1f355-f43a-43d3-8205-07df810b6a76</Data><Data></Data><Data></Data><Data>Unknown</Data><Binary>55006E006B006E006F0077006E0000000000</Binary></EventData></Event>
Ok, we have an application, some unstructured execution parameters, version strings, some opaque hex numbers. Cool cool... OOOOH Binary. Clearly that is where all the secrets lie! Lets decode it!
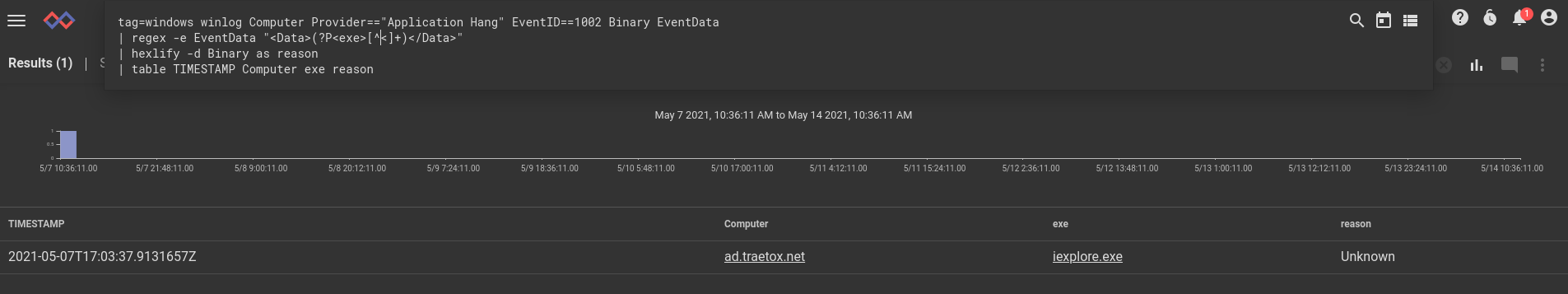
tag=windows winlog Computer Provider=="Application Hang" EventID==1002 Binary EventData
| regex -e EventData "<Data>(?P<exe>[^<]+)</Data>"
| hexlify -d Binary
| table TIMESTAMP Computer exe Binary
Soo... 55006E006B006E006F0077006E0000000000 decodes to "Unknown" in UTF-16. Thanks... And double thanks for the multiple NULL characters at the end.
Screenshots:
Next week we'll look at removable storage events; you know, the things that make your air gap NOT an airgap!
If you have retrieved this result from your logs and wish to discuss it with others, feel free to join our Discord and engage with our team of data experts.